Keystroke loggers capture passphrases before the data stream is encrypted | Download Scientific Diagram
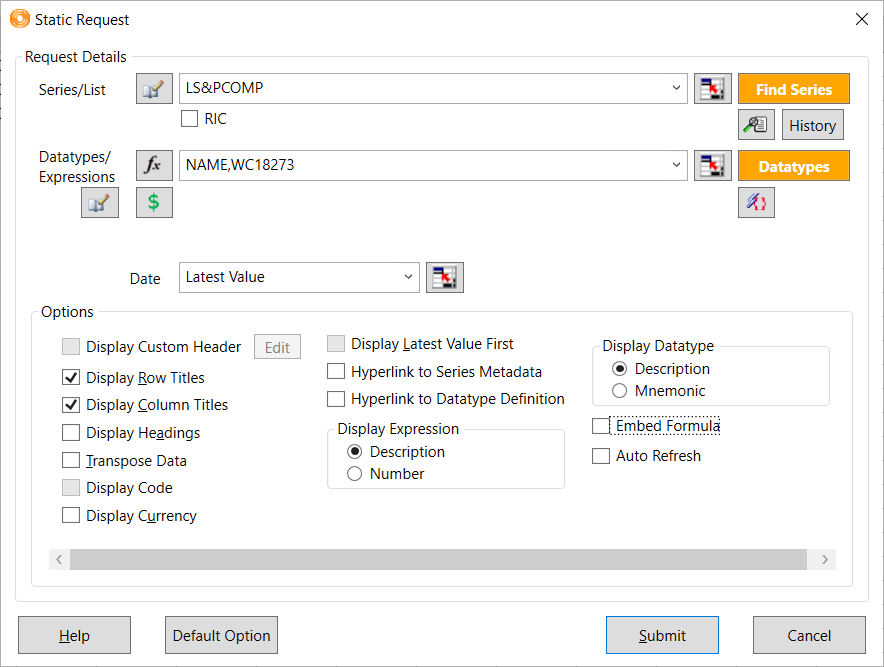
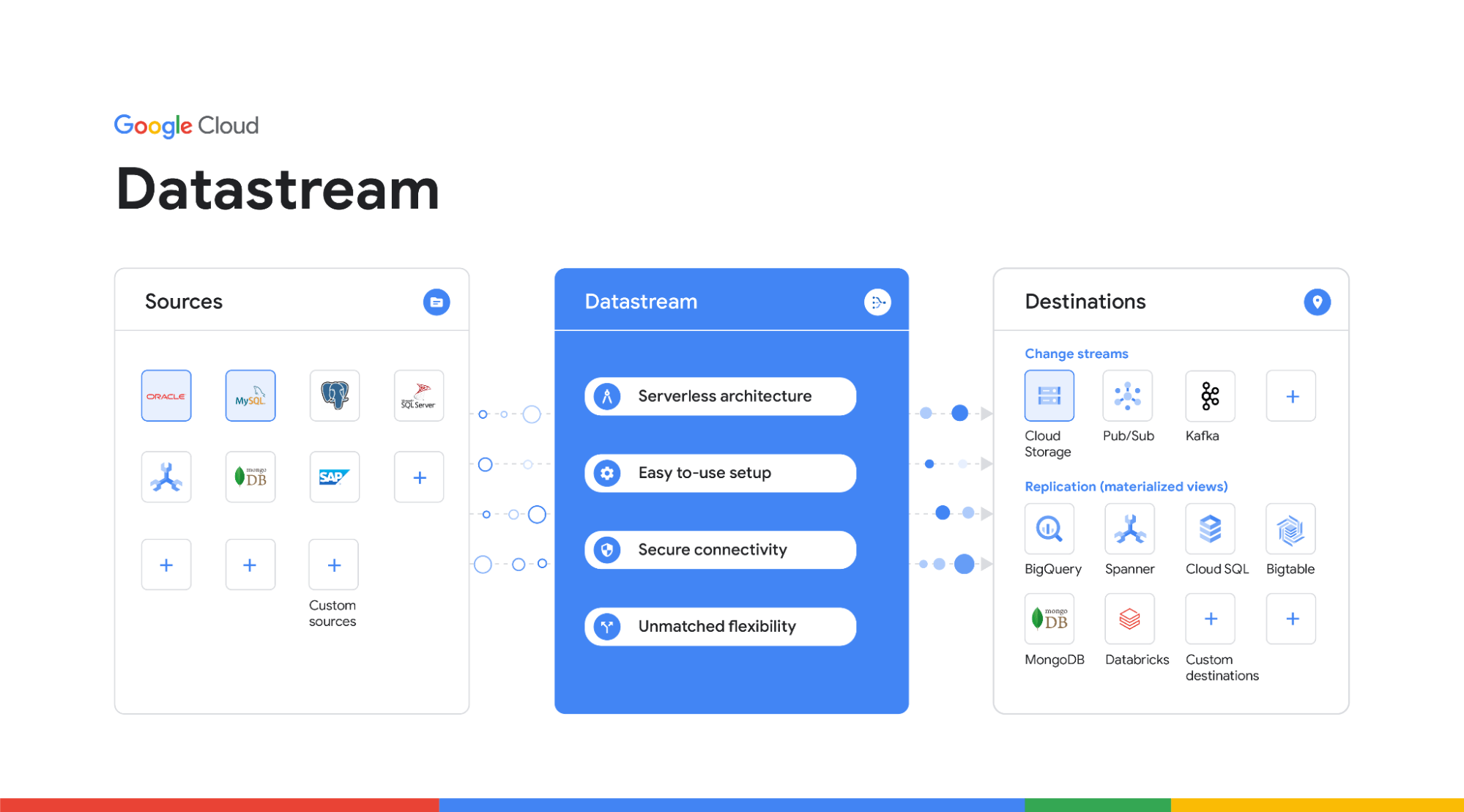
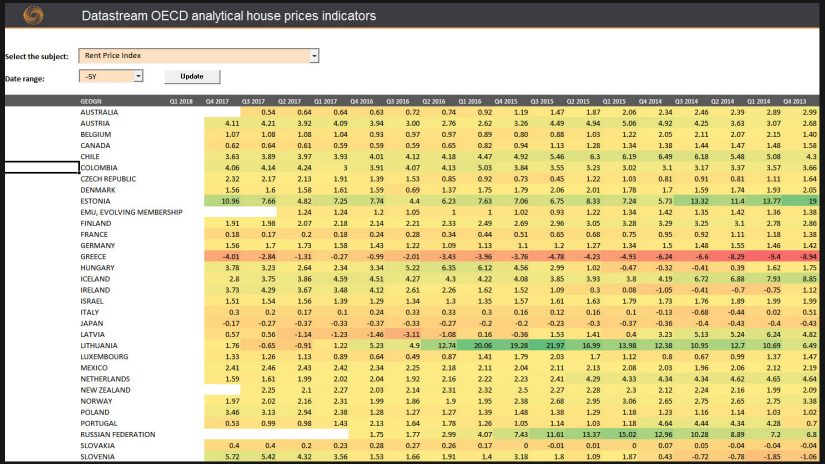
Introduction to Datastream via Eikon | by Specialist Library Support | Specialist Library Support | Medium
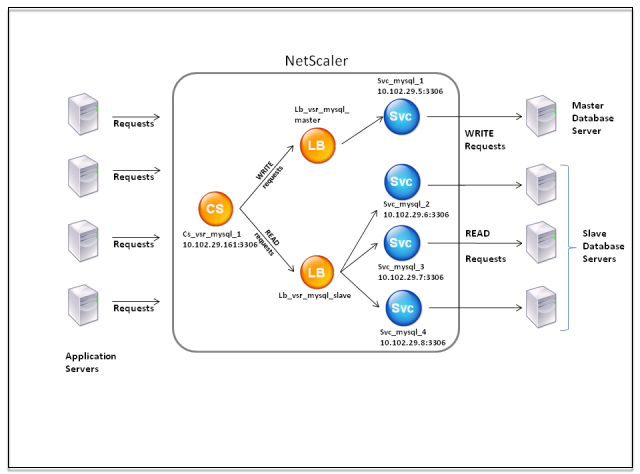
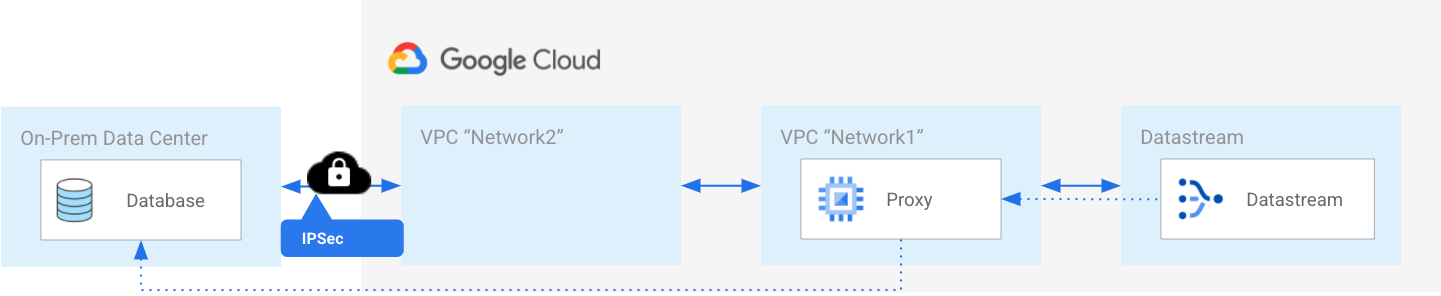
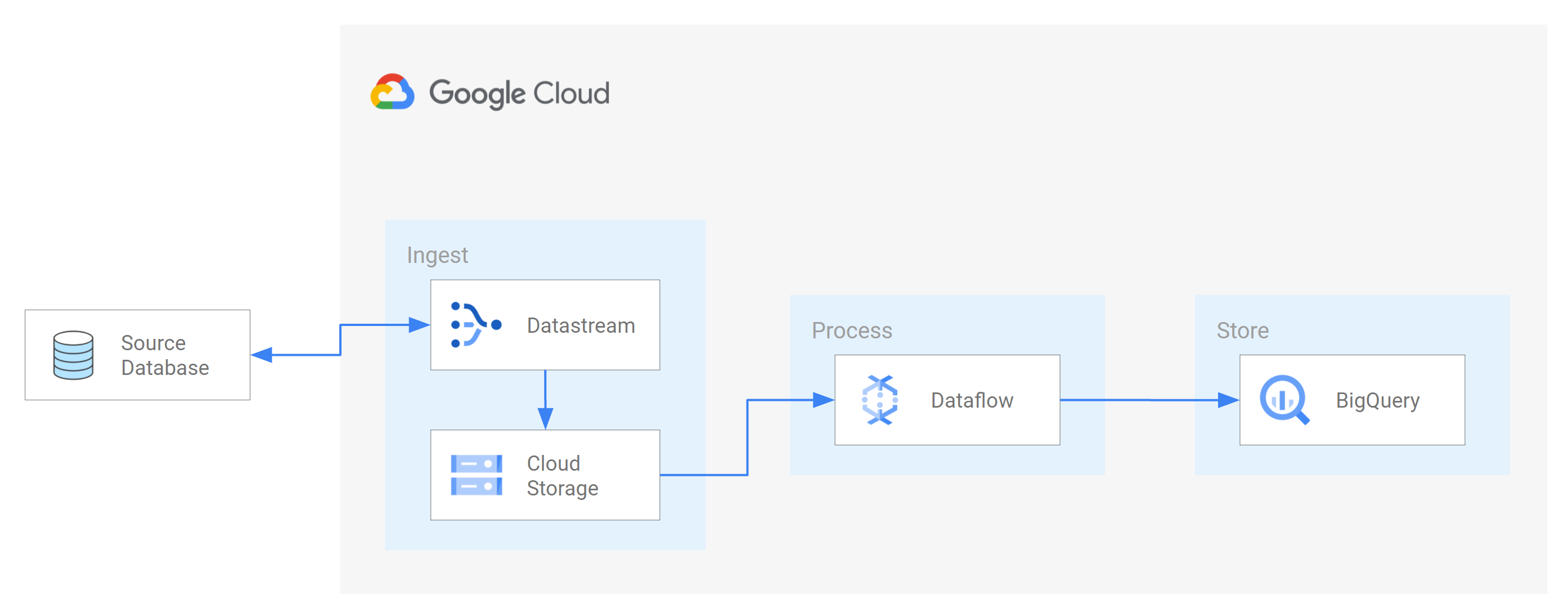
Cas d'utilisation 1 : Configuration de DataStream pour une architecture de base de données primaire/secondaire